Business Pie Chart. Growth Curve. Presentation Buttons. ATM Cash Machine Withdrawal Icons. Click Here, Check PIN Number, Processing And Cash Withdrawal Symbols. Data Analysis. Vector Royalty Free SVG, Cliparts, Vectors, And Stock

Human Pin code Analysis | The Enspirer🌻Iann, WhatsApp:072 321 4879 Full Human Pin Code Analysis. | By The Enspirer | Facebook | Hi folks, I'm the Inspirer, the Connection Therapist. All of
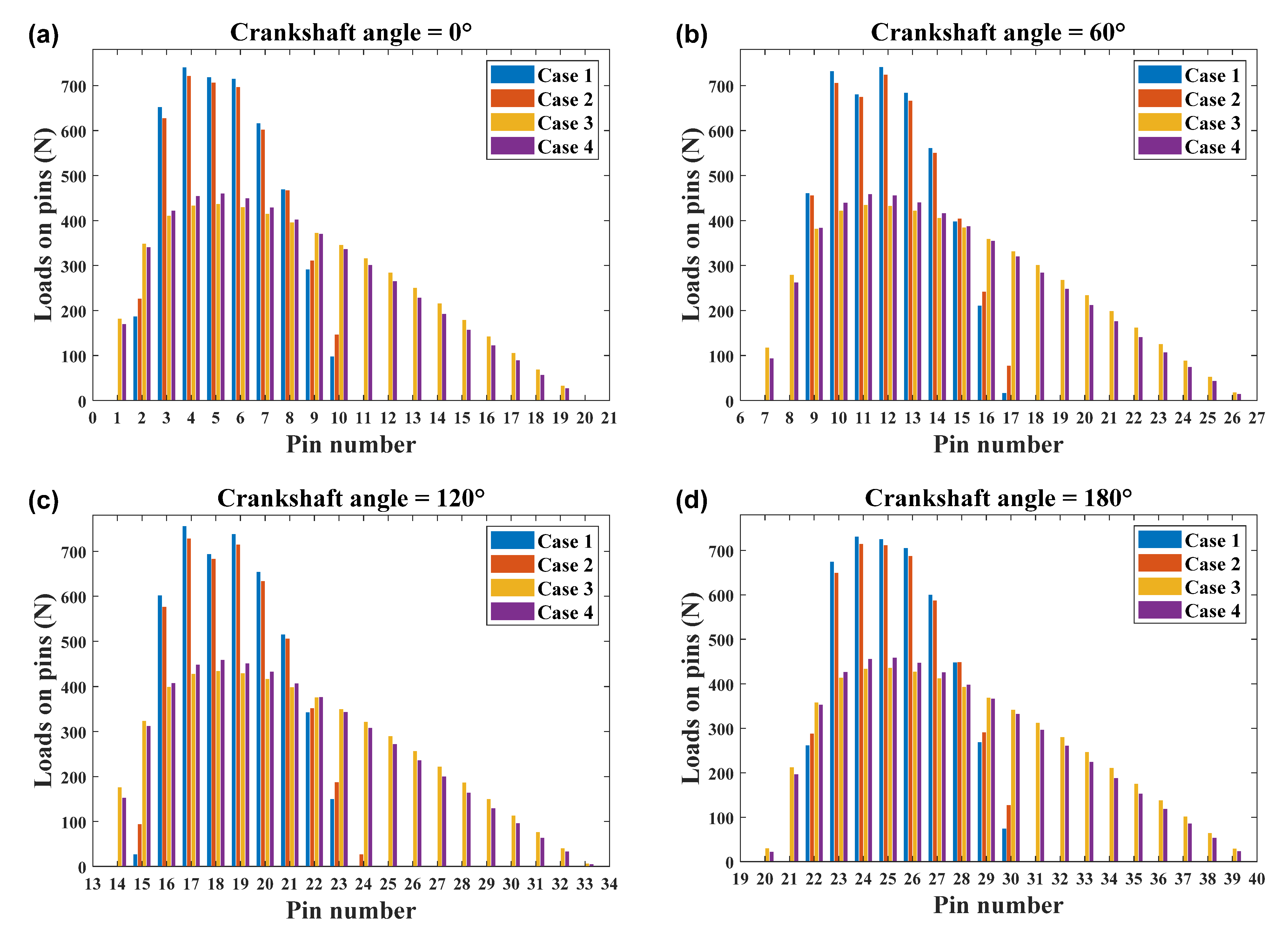
Machines | Free Full-Text | Design and Load Distribution Analysis of the Mismatched Cycloid-Pin Gear Pair in RV Speed Reducers

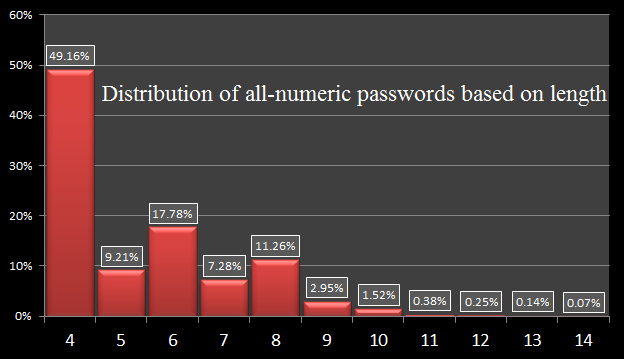
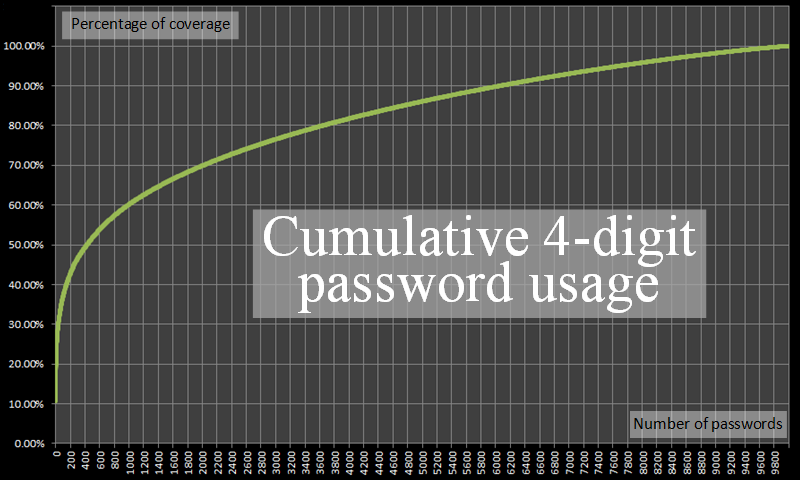
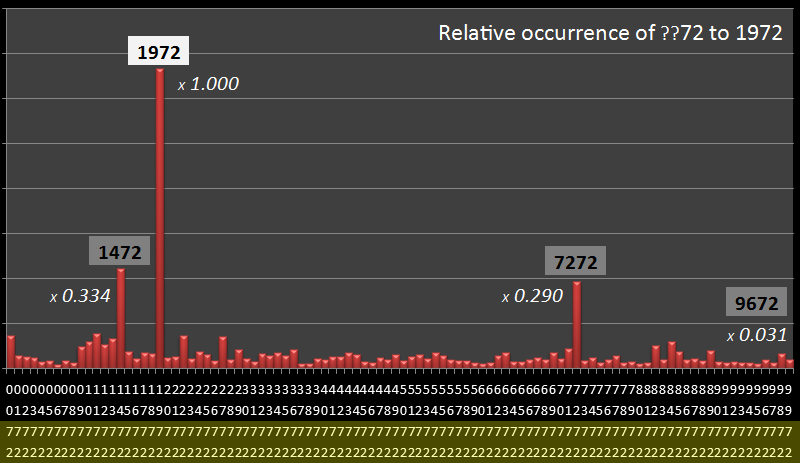
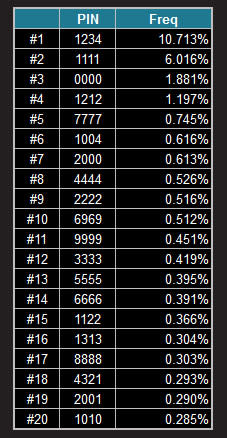
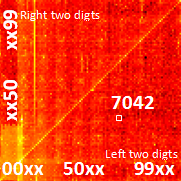
An analysis of chosen alarm code pin numbers & their weakness against a modified brute force attack | Semantic Scholar

An analysis of chosen alarm code pin numbers & their weakness against a modified brute force attack | Semantic Scholar








![The Most Common and Least Used 4-Digit PIN Numbers [Security Analysis Report] The Most Common and Least Used 4-Digit PIN Numbers [Security Analysis Report]](https://www.howtogeek.com/wp-content/uploads/gg/up/sshot506450451f9e6.jpg?height=200p&trim=2,2,2,2)